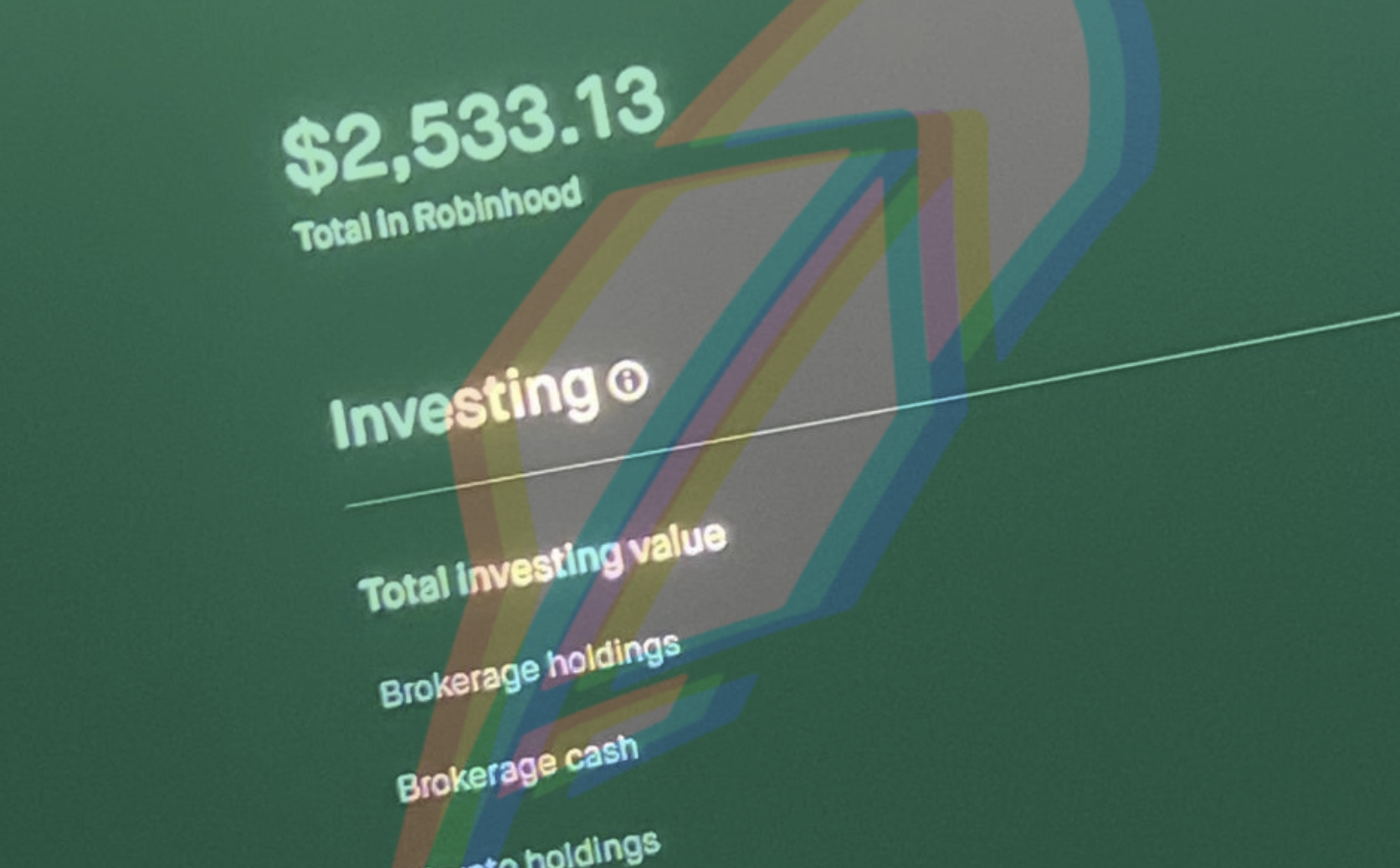
Hackers are targeting accounts on Robinhood, the popular online brokerage service, with the ultimate goal of stealing customer funds, according to a wide spanning review of criminal forums and Telegram groups by 404 Media. Hackers are also advertising compromised Robinhood accounts for sale as part of that process.
The news shows how a complex ecosystem of hackers all offering different services—harvesting the email address and passwords; expertise on moving the funds; and developers who make tools to intercept multi-factor authentication codes—all come together to target unsuspecting Robinhood users.
“Send me all yo Robinhoods. Instant cashout,” one message in a fraud-focused Telegram group reads. “Btw cashing all Robinhoods rn,” adds another.
Multiple members of subreddits related to Robinhood have reported their Robinhood accounts being compromised over the last few years. In some cases, the users reported the hackers withdrew funds.