TeleGuard, an app that markets itself as a secure, end-to-end encrypted messaging platform which has been downloaded more than a million times, implements its encryption so poorly that an attacker can trivially access a user’s private key and decrypt their messages, multiple security researchers told 404 Media. TeleGuard also uploads users’ private keys to a company server, meaning TeleGuard itself could decrypt its users’ messages, and the key can also at least partially be derived from simply intercepting a user’s traffic, the researchers found.
The news highlights something of the wild west of encrypted messaging apps, where not all are created equal.
“No storage of data. Highly encrypted. Swiss made,” the website for TeleGuard reads. The site also says, “The chats as well as voice and video calls are end-to-end encrypted.”
In March an anonymous security researcher, who didn’t provide their name, told 404 Media about a series of vulnerabilities in TeleGuard. They included the fact the TeleGuard app uploads users’ private encryption keys to the company’s server upon account registration.
Often when implementing encrypted messages, apps will assign users a public and private key. The public key is what other users use to encrypt messages for them, and the private key is what a user uses to decrypt messages meant for them. If this key falls into someone else’s hands, they may be able to read a users’ messages.
In true end-to-end encryption, this encryption happens on a user’s phone, and the key should never leave that device. With TeleGuard, the app is transmitting that highly sensitive key to the company’s servers. Technically, the app uploads an encrypted version of the private key, but it also transmits other information that allows the server to decrypt it, the researcher explained. That includes the user’s unique ID, which is also uploaded along with the key; a hardcoded salt (which in cryptography is supposed to be a random string of characters, but in this case is constant); and a hardcoded nonce (which is also supposed to be random for every communication to stop certain attacks, but is constant with TeleGuard). “The server can decrypt every user's private key. It has everything,” the researcher wrote in their findings shared with 404 Media.
That series of design decisions means TeleGuard, the company, receives users’ private keys. But the keys are also accessible to other attackers. The researcher found it’s possible to retrieve a specific user’s private key by simply plugging their user ID into TeleGuard’s API. Many people share their user ID publicly so they can be contacted, opening them up to this attack.
404 Media asked Dan Guido, CEO and co-founder of cybersecurity firm Trail of Bits, whether his team was able to verify the findings. Guido said the company found much the same thing, and added the app’s encryption “is meaningless,” because of the app uploading the private keys and the server’s ability to decrypt them.
Trail of Bits then found multiple other security issues with TeleGuard, including being able to at least partially extract users’ private keys from simply intercepting their traffic. Trail of Bits said it then successfully decrypted one of the shoddily encrypted private keys from that capture.
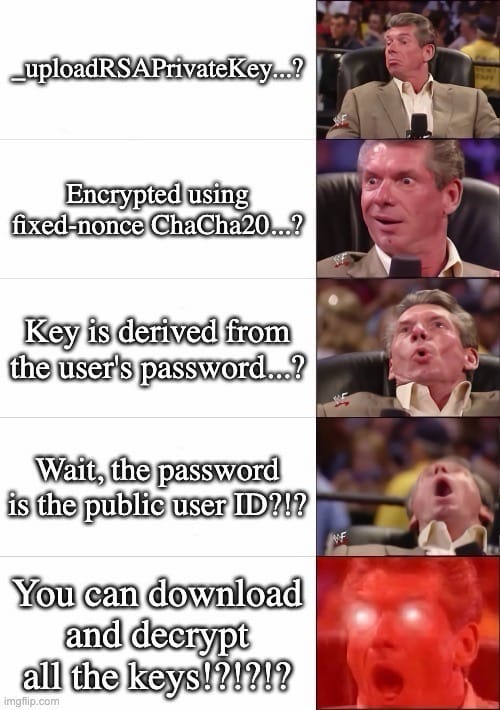
Guido sent 404 Media this meme:
The researcher who initially reached out also said TeleGuard’s metadata—when someone sent a message, and to whom—is in plaintext, meaning that could be exposed to attackers too.
TeleGuard launched in around 2021, according to archives of the app’s page on the Wayback Machine. It is made by Swisscows, a company that also makes what it describes as an anonymous search engine, a VPN, and an email service. In a promotional video, TeleGuard claims to have “one of the strongest encryptions available.”
Neither TeleGuard nor Swisscows responded to multiple requests for comment, nor gave any indication or timeline of when they might fix the issues.
TeleGuard has been recommended to cam models as a way to communicate, according to a post on a subreddit for models. The app has also repeatedly been linked to child abusers, with one local media outlet reporting TeleGuard is “notorious” among prosecutors for child sexual abuse material. The FBI previously obtained data about a TeleGuard user through push notifications sent to their phone. A foreign law enforcement agency had TeleGuard hand over push notification-related data, which the FBI then took to Google to obtain email addresses linked to that alleged pedophile, The Washington Post reported.


